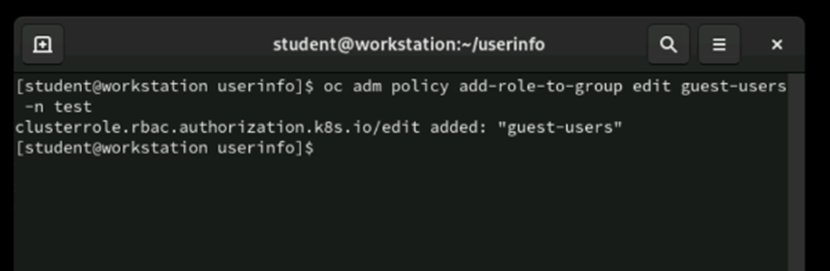
OpenShift RBAC and Self-Provisioner management
#Leave A Comment

Subscribe To Newsletter
Get Notification of each & every new blogs through your e-mail
This is a blog platform where I share my personal experiences and insights, encouraging others to share theirs as well so we can learn from each other and grow together
#Contact With Me
+8801973111031